Good morning, tech enthusiasts! ☀️ Today, we're sharpening our swords and delving into the fortress of Active Directory (AD) security. Brace yourselves for a journey through the "Active Directory Kill Chain Attack & Defense" 🛠️🔗, a master strategy developed by the wizards at Microsoft for diagnosing and deflecting AD attacks.
Each stage of an AD assault, from the sneaky reconnaissance 🕵️♂️ to the final triumph or defeat 🏁, demands a unique shield of defense. We're talking about ironclad password policies, impregnable network segmentation, and vigilant monitoring—essentially, your cybersecurity Swiss Army knife. 🗡️🔍 Understanding these intricate tactics and tools is crucial for IT gladiators 🛡️💻 in their quest to protect the realm of digital domains.
So, grab your coffee ☕ and settle in as we unravel this complex tapestry of cyber strategies, equipping you with the arsenal 🏹 you need to fortify your organization's bastions against the invisible siege of cyberspace. Let's turn the tide in this high-tech game of thrones! 🏰🎮


In an era where digital threats are as varied as they are frequent, understanding and responding to security incidents is crucial for safeguarding your organization's digital fortress. A security incident, differing from a mere event, disrupts normal operations and poses a risk to the integrity, availability, or confidentiality of your systems and data.
The Fine Line: Events vs. Incidents
While a high-severity security event might just be a fluke, like a single user being denied access, a security incident like a DoS attack impacts a larger user base and indicates a more serious problem.
Signs of Trouble
Be on the lookout for these red flags:
Privileged user anomalies: Unusual activities in high-level accounts could indicate a breach.
Unauthorized access attempts: These could range from strange login attempts to accessing unrelated data.
Outbound traffic irregularities: Watch out for large data uploads or downloads signaling data exfiltration.
Geographical inconsistencies: Traffic from or to unusual locations might point to external threats.
Resource overuse: Excessive consumption of server resources can indicate unauthorized access.
Common Attack Vectors
Attack vectors are numerous, but watch out for these prevalent ones:
External media and attrition attacks: These involve brute-force tactics from external devices.
Web and email-based attacks: Phishing and malware-infected sites or emails.
Improper usage: Violations of organizational policies by authorized users.
Drive-by downloads and ad-based malware: Automated downloads from compromised websites or apps.
Scareware: Tricking users into downloading malicious software under false pretenses.
To prevent a threat actor from gaining access to systems or data using an authorized user's account, implement MFA. This requires a user to provide a password, plus at least one additional piece of identifying information.
Additionally, encrypt sensitive corporate data at rest and as it travels over a network, using suitable software or hardware technology. That way, attackers aren't able to access confidential information.
2. Privilege escalation attack
An attacker who gains unauthorized access to an organization's network may then try to obtain higher-level privileges using what's known as a privilege escalation exploit. Successful privilege escalation attacks grant threat actors privileges that normal users don't have.
Typically, privilege escalation occurs when the threat actor takes advantage of a bug, misconfiguration, programming error or any vulnerability in an application or system to gain elevated access to protected data.
This usually occurs after a malicious hacker has already compromised a network by gaining access to a low-level user account and looks to gain higher-level privileges -- i.e., full access to an enterprise's IT system -- either to study the system further or perform an attack.
To decrease the risk of privilege escalation, organizations should look for and remediate security weak spots in their IT environments on a regular basis. They should also follow the principle of least privilege – i.e., limit the access rights for users to the bare-minimum permissions they need to do their jobs -- and implement security monitoring.
Organizations should also evaluate the risks to their sensitive data and take the necessary steps to secure that data.
3. Insider threat
This is a malicious or accidental threat to an organization's security or data typically attributed to employees; former employees; or third parties, including contractors, temporary workers or customers.
To detect and prevent insider threats, implement spyware scanning programs, antivirus programs, firewalls, and a rigorous data backup and archiving routine. In addition, train employees and contractors on security awareness before allowing them to access the corporate network. Implement employee monitoring software to reduce the risk of data breaches and the theft of intellectual property by identifying careless, disgruntled or malicious insiders.
4. Phishing attack
In a phishing attack, a threat actor masquerades as a reputable entity or person in an email or other communication channel. The attacker uses phishing emails to distribute malicious links or attachments that can perform a variety of functions, including extracting login credentials or account information from victims. A more targeted type of phishing attack known as spear phishing occurs when the attacker invests time researching the victim to pull off an even more successful attack.
Effective defense against phishing attacks starts with educating users to identify phishing messages. In addition, a gateway email filter can trap many mass-targeted phishing emails and reduce the number of phishing emails that reach users' inboxes.
5. Malware attack
This is a broad term for different types of malware that are installed on an enterprise's system. Malware includes Trojans, worms, ransomware, adware, spyware and various types of viruses. Some malware is inadvertently installed when an employee clicks on an ad, visits an infected website, or installs freeware or other software.
Signs of malware include unusual system activity, such as a sudden loss of disk space; unusually slow speeds; repeated crashes or freezes; an increase in unwanted internet activity; and pop-up advertisements. Installing an antivirus tool can detect and remove malware. These tools can either provide real-time protection or detect and remove malware by executing routine system scans.
6. DoS attack
A threat actor launches a denial-of-service (DoS) attack to shut down an individual machine or an entire network so that it's unable to respond to service requests. DoS attacks do this by flooding the target with traffic or sending it some information that triggers a crash.
An organization can typically deal with a DoS attack that crashes a server by simply rebooting the system. In addition, reconfiguring firewalls, routers and servers can block any bogus traffic. Keep routers and firewalls updated with the latest security patches.
Also, application front-end hardware that's integrated into the network can help analyze and screen data packets -- i.e., classify data as priority, regular or dangerous -- as they enter the system. The hardware can also help block threatening data.
7. Man-in-the-middle attack
A man-in-the-middle (MitM) attack is one in which the attacker secretly intercepts and alters messages between two parties who believe they are communicating directly with each other. In this attack, the attacker manipulates both victims to gain access to data. Examples of MitM attacks include session hijacking, email hijacking and Wi-Fi eavesdropping.
Although it's difficult to detect MitM attacks, there are ways to prevent them. One way is to implement an encryption protocol, such as TLS, that provides authentication, privacy and data integrity between two communicating computer applications. Another encryption protocol is SSH, a network protocol that gives users, particularly system administrators, a secure way to access a computer over an insecure network.
Enterprises should also educate employees to the dangers of using open public Wi-Fi, as it's easier for hackers to hack these connections. Organizations should also tell their workers to pay attention to warnings from browsers that sites or connections may not be legitimate. Companies should also use VPNs to help ensure secure connections.
8. Password attack
This type of attack is aimed specifically at obtaining a user's password or an account's password. To do this, malicious hackers use a variety of methods, including password-cracking programs, dictionary attacks, password sniffers and guessing passwords via brute force -- i.e., trial and error.
A password cracker is an application program used to identify an unknown or forgotten password for a computer or network resources. This helps an attacker obtain unauthorized access to resources. A dictionary attack is a method of breaking into a password-protected computer or server by systematically entering every word in a dictionary as a password.
To prevent password attacks, organizations should adopt MFA for user validation. In addition, users should choose strong passwords that include at least seven characters, as well as a mix of upper and lowercase letters, numbers and symbols. Users should change their passwords regularly and use different passwords for different accounts. In addition, organizations should use encryption on any passwords stored in secure repositories.
9. Web application attack
This is any incident in which a web application is the vector of the attack, including exploits of code-level vulnerabilities in the application, as well as thwarting authentication mechanisms. One example of a web application attack is a cross-site scripting attack. This is a type of injection security attack in which an attacker injects data, such as a malicious script, into content from otherwise trusted websites.
Enterprises should review code early in the development phase to detect vulnerabilities; static and dynamic code scanners can automatically check for these. Also, implement bot detection functionality to prevent bots from accessing application data. Finally, a web application firewall (WAF) can monitor a network and block potential attacks.
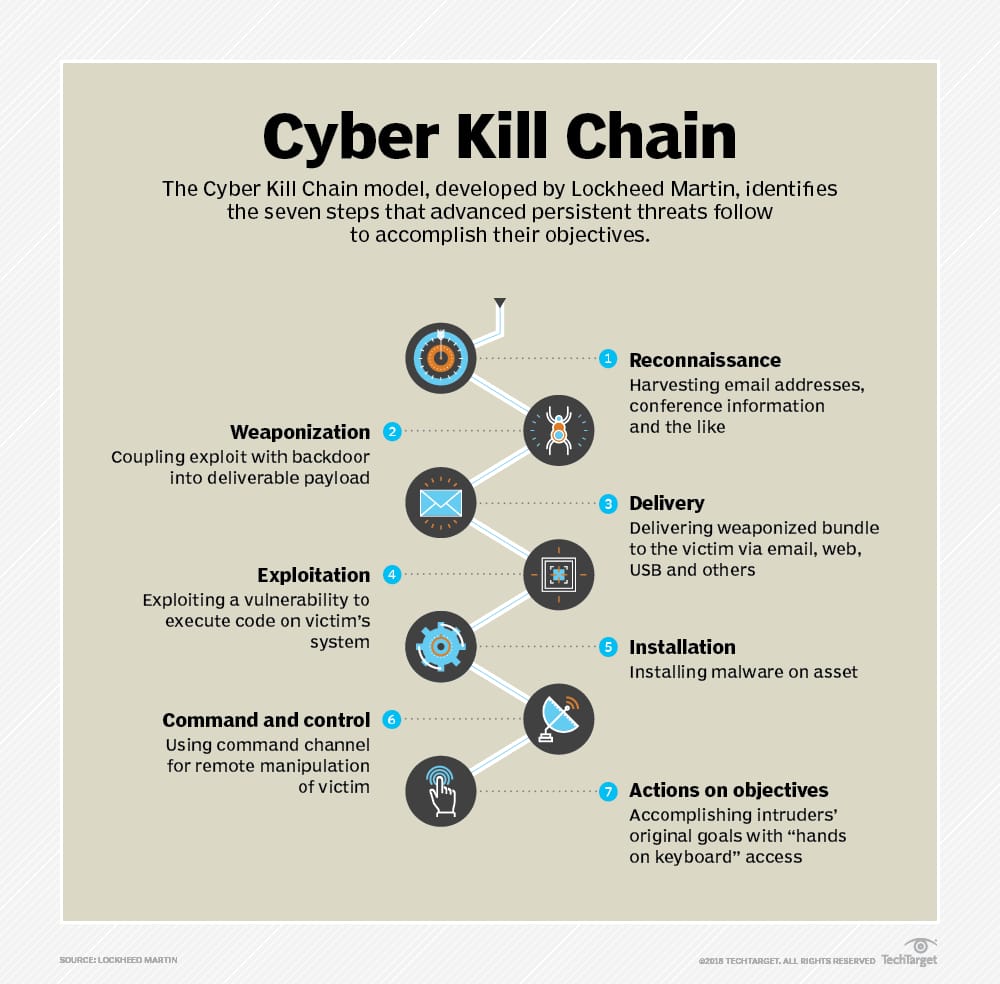
10. Advanced persistent threat
An advanced persistent threat (APT) is a prolonged and targeted cyberattack typically executed by sophisticated cybercriminals or nation-states. In this attack, the intruder gains access to a network and remains undetected for an extended period of time. The APT's goal is usually to monitor network activity and steal data rather than cause damage to the network or organization.
Monitoring incoming and outgoing traffic can help organizations prevent hackers from installing backdoors and extracting sensitive data. Enterprises should also install WAFs at the edge of their networks to filter traffic coming into their web application servers. This can help filter out application layer attacks, such as SQL injection attacks, often used during the APT infiltration phase. Additionally, a network firewall can monitor internal traffic.

Active Directory Kill Chain: Defense Checklist and Tools 2024
Active Directory (AD), a cornerstone of corporate network security, faces evolving threats. The "Active Directory Kill Chain Attack & Defense" framework offers a structured approach to understanding and countering these threats. Here's your essential guide to fortify AD against cyber assaults.
Stages of AD Attacks and Defenses
Reconnaissance: Attackers gather network information. Defense: Limit exposure, segment networks, and monitor directory visibility.
Initial Compromise: Exploiting vulnerabilities for access. Defense: Strong passwords, patching, awareness training, and multi-factor authentication.
Establish Foothold: Creating backdoors or malware installation. Defense: Endpoint detection, regular audits, and activity monitoring.
Escalation of Privilege: Targeting higher-level privileges. Defense: Least privilege principle, privilege audits, and privileged access management.
Internal Reconnaissance: Exploring for high-value targets. Defense: Network segmentation, traffic monitoring, and intrusion detection systems.
Move Laterally: Accessing other systems in the network. Defense: Strict access controls, monitoring lateral movements, and network security tools.
Maintain Presence: Ensuring ongoing network access. Defense: Continuous monitoring, network scans, and incident response plans.
Complete Mission: Achieving data exfiltration or disruption. Defense: Data loss prevention tools, regular backups, and incident response strategy.
Securing Active Directory: Your Checklist
Regular updates and patches.
Secure and dedicated domain controllers.
Robust password policies and MFA.
Monitor user accounts, especially unused or overprivileged ones.
Limit privileged accounts.
Audit logins and activities.
Secure network access to AD with firewalls and network segmentation.
Use Organizational Units and Group Policies effectively.
Regular backups and disaster recovery planning.
Educate users on phishing and social engineering threats.
Regular security audits for AD compliance.
Deploy advanced security solutions like SIEM, IDS/IPS.
Strengthen AD configurations.
Control physical access to servers and network equipment.
Stay informed about emerging threats and adjust security measures accordingly.
Discovery
SPN Scanning
Data Mining
User Hunting
LAPS
AppLocker
Active Directory Federation Services
Privilege Escalation
Abusing Active Directory Certificate Services
PetitPotam
Zerologon
Passwords in SYSVOL & Group Policy Preferences
MS14-068 Kerberos Vulnerability
DNSAdmins
Kerberos Delegation
Unconstrained Delegation
Constrained Delegation
Resource-Based Constrained Delegation
Insecure Group Policy Object Permission Rights
Insecure ACLs Permission Rights
Domain Trusts
DCShadow
RID
Microsoft SQL Server
Red Forest
Exchange
NTLM Relay & LLMNR/NBNS
Lateral Movement
Microsoft SQL Server Database links
Pass The Hash
System Center Configuration Manager (SCCM)
WSUS
Password Spraying
Automated Lateral Movement
Defense Evasion
In-Memory Evasion
Endpoint Detection and Response (EDR) Evasion
OPSEC
Microsoft ATA & ATP Evasion
PowerShell ScriptBlock Logging Bypass
PowerShell Anti-Malware Scan Interface (AMSI) Bypass
Loading .NET Assemblies Anti-Malware Scan Interface (AMSI) Bypass
AppLocker & Device Guard Bypass
Sysmon Evasion
HoneyTokens Evasion
Disabling Security Tools
Credential Dumping
NTDS.DIT Password Extraction
SAM (Security Accounts Manager)
Kerberoasting
Kerberos AP-REP Roasting
Windows Credential Manager/Vault
DCSync
LLMNR/NBT-NS Poisoning
Others
Persistence
Golden Ticket
SID History
Silver Ticket
DCShadow
AdminSDHolder
Group Policy Object
Skeleton Keys
SeEnableDelegationPrivilege
Security Support Provider
Directory Services Restore Mode
ACLs & Security Descriptors
Tools & Scripts
Certify – Certify is a C# tool to enumerate and abuse misconfigurations in Active Directory Certificate Services (AD CS).
PSPKIAudit – PowerShell toolkit for auditing Active Directory Certificate Services (AD CS).
PowerView – Situational Awareness PowerShell framework
BloodHound – Six Degrees of Domain Admin
Impacket – Impacket is a collection of Python classes for working with network protocols
aclpwn.py – Active Directory ACL exploitation with BloodHound
CrackMapExec – A swiss army knife for pentesting networks
ADACLScanner – A tool with GUI or command linte used to create reports of access control lists (DACLs) and system access control lists (SACLs) in Active Directory
zBang – zBang is a risk assessment tool that detects potential privileged account threats
SafetyKatz – SafetyKatz is a combination of slightly modified version of @gentilkiwi’s Mimikatz project and @subTee’s .NET PE Loader.
SharpDump – SharpDump is a C# port of PowerSploit’s Out-Minidump.ps1 functionality.
PowerUpSQL – A PowerShell Toolkit for Attacking SQL Server
Rubeus – Rubeus is a C# toolset for raw Kerberos interaction and abuses
ADRecon – A tool which gathers information about the Active Directory and generates a report which can provide a holistic picture of the current state of the target AD environment
Mimikatz – Utility to extract plaintexts passwords, hash, PIN code and kerberos tickets from memory but also perform pass-the-hash, pass-the-ticket or build Golden tickets
Grouper – A PowerShell script for helping to find vulnerable settings in AD Group Policy.
Powermad – PowerShell MachineAccountQuota and DNS exploit tools
RACE – RACE is a PowerShell module for executing ACL attacks against Windows targets.
DomainPasswordSpray – DomainPasswordSpray is a tool written in PowerShell to perform a password spray attack against users of a domain.
MailSniper – MailSniper is a penetration testing tool for searching through email in a Microsoft Exchange environment for specific terms (passwords, insider intel, network architecture information, etc.)
LAPSToolkit – Tool to audit and attack LAPS environments.
CredDefense – Credential and Red Teaming Defense for Windows Environments
ldapdomaindump – Active Directory information dumper via LDAP
SpoolSample – PoC tool to coerce Windows hosts authenticate to other machines via the MS-RPRN RPC interface
adconnectdump – Azure AD Connect password extraction
o365recon – Script to retrieve information via O365 with a valid cred
ROADtools – ROADtools is a framework to interact with Azure AD.
Stormspotter – Stormspotter creates an “attack graph” of the resources in an Azure subscription.
AADInternals – AADInternals is PowerShell module for administering Azure AD and Office 365
MicroBurst: A PowerShell Toolkit for Attacking Azure – MicroBurst includes functions and scripts that support Azure Services discovery, weak configuration auditing, and post exploitation actions such as credential dumping.
Ebooks
Cheat Sheets
Tools Cheat Sheets – Tools (PowerView, PowerUp, Empire, and PowerSploit)
Other Resources
Azure Active Directory
Defense & Detection
Tools & Scripts
Invoke-TrimarcADChecks – The Invoke-TrimarcADChecks.ps1 PowerShell script is designed to gather data from a single domain AD forest to performed Active Directory Security Assessment (ADSA).
Create-Tiers in AD – Project Title Active Directory Auto Deployment of Tiers in any environment
SAMRi10 – Hardening SAM Remote Access in Windows 10/Server 2016
Net Cease – Hardening Net Session Enumeration
PingCastle – A tool designed to assess quickly the Active Directory security level with a methodology based on risk assessment and a maturity framework
Aorato Skeleton Key Malware Remote DC Scanner – Remotely scans for the existence of the Skeleton Key Malware
Reset the krbtgt account password/keys – This script will enable you to reset the krbtgt account password and related keys while minimizing the likelihood of Kerberos authentication issues being caused by the operation
RiskySPN – RiskySPNs is a collection of PowerShell scripts focused on detecting and abusing accounts associated with SPNs (Service Principal Name).
Deploy-Deception – A PowerShell module to deploy active directory decoy objects
SpoolerScanner – Check if MS-RPRN is remotely available with powershell/c#
dcept – A tool for deploying and detecting use of Active Directory honeytokens
LogonTracer – Investigate malicious Windows logon by visualizing and analyzing Windows event log
DCSYNCMonitor – Monitors for DCSYNC and DCSHADOW attacks and create custom Windows Events for these events
Sigma – Generic Signature Format for SIEM Systems
Sysmon – System Monitor (Sysmon) is a Windows system service and device driver that, once installed on a system, remains resident across system reboots to monitor and log system activity to the Windows event log.
SysmonSearch – Investigate suspicious activity by visualizing Sysmon’s event log
ClrGuard – ClrGuard is a proof of concept project to explore instrumenting the Common Language Runtime (CLR) for security purposes.
Get-ClrReflection – Detects memory-only CLR (.NET) modules.
Get-InjectedThread – Get-InjectedThread looks at each running thread to determine if it is the result of memory injection.
SilkETW – SilkETW & SilkService are flexible C# wrappers for ETW, they are meant to abstract away the complexities of ETW and give people a simple interface to perform research and introspection.
WatchAD – AD Security Intrusion Detection System
Sparrow – CISA’s Cloud Forensics team created Sparrow.ps1 to help detect possible compromised accounts and applications in the Azure/m365 environment.
DFIR-O365RC – The DFIR-O365RC PowerShell module is a set of functions that allow the DFIR analyst to collect logs relevant for Office 365 Business Email Compromise investigations.
AzureADIncidentResponse – Tooling to assist in Azure AD incident response
ADTimeline – The ADTimeline script generates a timeline based on Active Directory replication metadata for objects considered of interest.
Sysmon Configuration
sysmon-modular – A Sysmon configuration repository for everybody to customise
sysmon-dfir – Sources, configuration and how to detect evil things utilizing Microsoft Sysmon.
sysmon-config – Sysmon configuration file template with default high-quality event tracing
Active Directory Security Checks (by Sean Metcalf – @Pyrotek3)
General Recommendations
Manage local Administrator passwords (LAPS).
Implement RDP Restricted Admin mode (as needed).
Remove unsupported OSs from the network.
Monitor scheduled tasks on sensitive systems (DCs, etc.).
Ensure that OOB management passwords (DSRM) are changed regularly & securely stored.
Use SMB v2/v3+
Default domain Administrator & KRBTGT password should be changed every year & when an AD admin leaves.
Remove trusts that are no longer necessary & enable SID filtering as appropriate.
All domain authentications should be set (when possible) to: “Send NTLMv2 response onlyrefuse LM & NTLM.”
Block internet access for DCs, servers, & all administration systems.
Protect Admin Credentials
No “user” or computer accounts in admin groups.
Ensure all admin accounts are “sensitive & cannot be delegated”.
Add admin accounts to “Protected Users” group (requires Windows Server 2012 R2 Domain Controllers, 2012R2 DFL for domain protection).
Disable all inactive admin accounts and remove from privileged groups.
Protect AD Admin Credentials
Limit AD admin membership (DA, EA, Schema Admins, etc.) & only use custom delegation groups.
‘Tiered’ Administration mitigating credential theft impact.
Ensure admins only logon to approved admin workstations & servers.
Leverage time-based, temporary group membership for all admin accounts
Protect Service Account Credentials
Limit to systems of the same security level.
Leverage “(Group) Managed Service Accounts” (or PW >20 characters) to mitigate credential theft (kerberoast).
Implement FGPP (DFL =>2008) to increase PW requirements for SAs and administrators.
Logon restrictions – prevent interactive logon & limit logon capability to specific computers.
Disable inactive SAs & remove from privileged groups.
Protect Resources
Segment network to protect admin & critical systems.
Deploy IDS to monitor the internal corporate network.
Network device & OOB management on separate network.
Protect Domain Controller
Only run software & services to support AD.
Minimal groups (& users) with DC admin/logon rights.
Ensure patches are applied before running DCPromo (especially MS14-068 and other critical patches).
Validate scheduled tasks & scripts.
Protect Workstations (& Servers)
Patch quickly, especially privilege escalation vulnerabilities.
Deploy security back-port patch (KB2871997).
Set Wdigest reg key to 0 (KB2871997/Windows 8.1/2012R2+): HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlSecurityProvidersWdigest
Deploy workstation whitelisting (Microsoft AppLocker) to block code exec in user folders – home dir & profile path.
Deploy workstation app sandboxing technology (EMET) to mitigate application memory exploits (0-days).
Logging
Enable enhanced auditing
“Audit: Force audit policy subcategory settings (Windows Vista or later) to override audit policy category settings”
Enable PowerShell module logging (“*”) & forward logs to central log server (WEF or other method).
Enable CMD Process logging & enhancement (KB3004375) and forward logs to central log server.
SIEM or equivalent to centralize as much log data as possible.
User Behavioural Analysis system for enhanced knowledge of user activity (such as Microsoft ATA).
Security Pro’s Checks
Identify who has AD admin rights (domain/forest).
Identify who can logon to Domain Controllers (& admin rights to virtual environment hosting virtual DCs).
Scan Active Directory Domains, OUs, AdminSDHolder, & GPOs for inappropriate custom permissions.
Ensure AD admins (aka Domain Admins) protect their credentials by not logging into untrusted systems (workstations).
Limit service account rights that are currently DA (or equivalent).

